Cyber threats rarely announce themselves ahead of time. For many businesses, the first sign of trouble is a sudden slowdown, locked files, or systems that simply stop working. When that happens, productivity drops, employees are left waiting, and the focus shifts from daily operations to damage control.
For a long time, many small and mid-sized businesses handled IT problems only when something went wrong. This reactive approach may have worked in the past, but it leaves little room to prevent issues before they escalate. Today’s threat landscape moves too quickly for businesses to rely on fixes after the fact.
A proactive approach focuses on preventing problems instead of reacting to them. With the right planning and oversight, businesses can detect unusual activity early and address vulnerabilities before they cause serious damage. Working with a Seattle managed IT services expert can help organizations build this kind of structure without needing a full internal IT department.
Key Takeaways
- Reactive IT leads to higher costs and longer downtime.
- Proactive monitoring helps detect threats earlier.
- Human error plays a major role in security incidents.
- Managed services provide enterprise-level tools at a smaller scale.
The Fundamental Shift: From Reactive to Proactive IT
To understand the value of proactive defense, it helps to compare it with the traditional break-fix approach.
The Reactive Model
In a reactive setup, businesses address problems only after they appear. When systems fail or malware spreads, an IT provider is called in to resolve the issue. While this may seem cost-effective at first, the real expense often comes from lost productivity and emergency service costs.
By the time an issue is discovered, employees may already be unable to work. Files may be lost, systems may need rebuilding, and operations may be interrupted for hours or even days.
The Proactive Model
Proactive IT focuses on prevention. Instead of waiting for failures, systems are monitored continuously and updated regularly. Potential threats are identified early, often before users notice anything is wrong.
This approach treats technology as an essential part of the business rather than a background utility. Regular maintenance, monitoring, and planning reduce the likelihood of major disruptions.
Changing the Mindset
Some businesses assume proactive security is only necessary for large organizations. In reality, smaller companies often face greater risk because they have fewer resources to recover from a major incident.
Adopting a proactive mindset means focusing on prevention instead of recovery. Even simple steps like regular updates and monitoring can make a significant difference in overall security.
The Financial Impact of Waiting Too Long
One reason businesses delay proactive security is cost. Monthly service fees may seem unnecessary compared to paying only when something breaks. However, reactive IT often leads to unpredictable and larger expenses over time.
Predictable Costs vs Emergency Spending
Emergency repairs can be expensive, especially when they require immediate attention. These costs often come without warning, making budgeting difficult.
Proactive services typically operate on a predictable schedule. This allows businesses to plan their expenses and avoid sudden financial strain caused by unexpected failures.
The Cost of Downtime
The most significant cost of IT issues is often downtime. When employees cannot access systems, work stops. Even a short disruption can affect productivity across an entire organization.
Downtime may also impact customer relationships. Delays in communication or service can reduce trust and create long-term challenges.
According to research from IBM, the average cost of a data breach reached $4.88 million in 2024. While many smaller organizations will not experience losses at that scale, even a fraction of that cost can be devastating.
Protecting Business Stability
From a risk management perspective, proactive security helps reduce uncertainty. Instead of waiting for a major issue, businesses can address vulnerabilities early and maintain stable operations.
This kind of protection allows leaders to focus on growth instead of constantly preparing for the next potential disruption.
The Core Elements of Proactive Defense
Proactive defense is built on several key practices that work together to reduce risk and improve reliability.
Continuous Monitoring
Cyber threats can appear at any time. Continuous monitoring helps detect unusual behavior as soon as it occurs.
Monitoring systems track activity across the network and identify patterns that may indicate a problem. When something unusual is detected, alerts are generated so the issue can be addressed quickly.
Automation also plays an important role. Some systems can respond immediately by limiting access or isolating affected devices.
Organizations that use automated detection often identify and contain threats faster than those relying on manual processes.
Regular Updates and Patch Management
Software updates often include security fixes that address newly discovered vulnerabilities. Delaying these updates leaves systems exposed to known risks.
Patch management ensures that operating systems and applications remain up to date. This process reduces the number of entry points available to attackers.
Without a structured update process, important patches may be missed or delayed. Over time, this increases the likelihood of a successful attack.
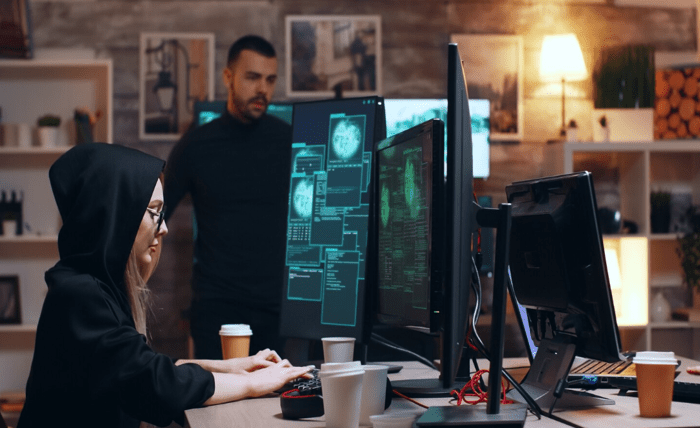
Strengthening the Human Element
Technology alone cannot prevent every security issue. Employees play a critical role in maintaining a secure environment.
Many incidents begin with simple mistakes, such as clicking on suspicious links or using weak passwords. Training helps employees recognize potential threats and respond appropriately.
Security awareness programs often include simulated phishing emails and practical guidance on identifying suspicious activity. These exercises help reinforce good habits and reduce risk.
Encouraging employees to report unusual activity also improves response times and helps prevent small issues from becoming larger problems.
Making Proactive Security Practical
Some businesses assume that proactive security requires a large internal team. In many cases, this is not necessary.
Managed service providers make advanced tools and expertise more accessible. Instead of building an internal department, businesses can work with experienced professionals who handle monitoring and maintenance.
This approach allows smaller organizations to benefit from the same types of protections used by larger companies.
Supporting Internal Teams
Businesses with internal IT staff can also benefit from additional support. External providers can assist with monitoring and maintenance, allowing internal teams to focus on strategic projects.
This collaboration helps ensure that important security tasks are handled consistently.
Flexible Support Options
Different organizations require different levels of support. Some need full-service management, while others only require assistance with specific areas.
Flexible service models allow businesses to choose the level of support that fits their needs. This makes proactive security more practical and easier to maintain over time.
Conclusion
Cyber threats continue to evolve, and reactive approaches are no longer enough to keep businesses safe. Waiting for problems to appear often leads to higher costs and longer disruptions.
Proactive defense focuses on prevention through monitoring, updates, and employee awareness. These practices help reduce risk and improve operational stability.
By taking steps to strengthen security before issues arise, businesses can protect their systems, maintain productivity, and reduce the likelihood of costly disruptions.